One upcoming feature is the ransomware canary file. The idea is that UrBackup generates a random file that looks like a file that potential ransomware should definitely encrypt. The backup server then checks if this file was changed or deleted during every backup. If ransomware encrypts the file the backup server will notice, fail backups and the backup server admin will get notified via alerts, can easily see the last known good backup and those good backup won’t get replaced by bad backups (backups with ransomware encrypted files).
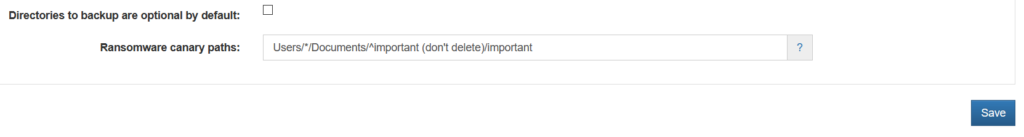
The setting to configure this is only present on the server. For example it would be set to
Users/*/Documents/^important (don’t delete)/important
Clients would go into the „Users“ backup path, descend into all „Documents“ directories below any folder directly below „Users“. Create a „important (don’t delete)“ folder if it doesn’t exist yet (that’s what the caret does). Then create a (random) „important-[SERVER TOKEN].docx“ canary file in that folder. The owner of the folder and file is set intelligently to the owner of sibling files or parent folders.
For now it is a very basic implementation. I.e.,
- It only uses a „docx“ file
- The template „docx“ is bundled with the client and only minimally modified on each client
- Only works with file backups
If a user moves, deletes or modifies a canary file the remedy to get backups working again would be to set the canary paths to empty for one file backup.
Thoughts? Improvement ideas?

Presumably leaving the path empty permanently would disable the feature?
How does it behave if a client removes or deletes an entire user account? (Transient & short term users).
Yes, it wouldn’t delete the files though. It would just stop checking them.
It would error… idk how it would differentiate between a removal on purpose vs. malicious removal.
I would recommend to inlude a client specific part in the filename. This would make it harder for an attacker to identify patterns in the filesystem when he has compromised multiple machines in the network. It can become pretty obvious that identical files in the same folder on every single client are in fact the canary.
I think it is a great idea.
Thanks Martin,
works on LockFile Ransomware ?